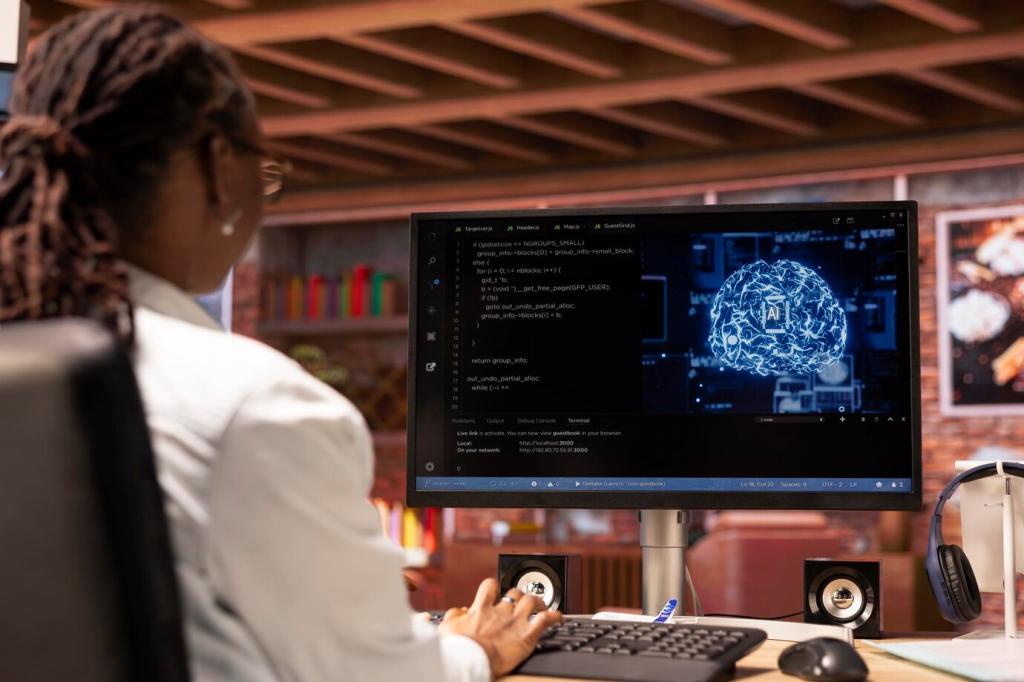
Security Innovations in Smart Living Spaces
Chosen theme: Security Innovations in Smart Living Spaces. Step inside a home where locks learn, networks adapt, and privacy is designed in from the ground up. We explore practical breakthroughs that protect families, simplify daily routines, and keep your data yours—without dulling the magic of a truly smart home.
The New Home Perimeter: From Doors to Data Streams

Sensor Fusion Guards the Invisible
Modern homes blend motion, contact, power, and environmental sensors to spot patterns a single device would miss. When a window opens and power draw spikes unexpectedly, your system correlates signals and nudges you with context, not noise. Tell us what signals you trust most, and why.

Network Segmentation as a Digital Moat
A separate network for IoT devices, WPA3 on Wi‑Fi, and restrictive firewall rules turn your home into compartments rather than a single vulnerable space. If a smart bulb misbehaves, it stays quarantined. Share your segmentation setup, and we’ll feature practical layouts next week.
Real Story: A False Alarm That Taught Precision
At 2 a.m., a family’s siren blared after their cat triggered motion. Sensor fusion corrected the problem: motion plus door status plus power usage must align before alerts escalate. Since then, only real anomalies wake them. What late‑night lesson improved your own setup?
Zero‑Trust Principles for Households
01
Strong Identity for Things, Not Just People
Devices can use certificates and mutual authentication so only known members join your home fabric. Standards like Matter emphasize cryptographic onboarding, reducing rogue device risks. Have you tried QR‑based commissioning or code‑verified pairing? Tell us what worked and what needs friendlier guidance.
02
Least‑Privilege Automation Rules
Let routines control exactly what they must, and nothing else. A lighting scene should not access cameras; a weather widget shouldn’t touch door locks. Mapping each routine’s minimal permissions keeps convenience intact and abuse unlikely. Want a printable checklist? Subscribe and we’ll send you one.
03
Continuous Verification Beats One‑Time Trust
Even after onboarding, devices should prove they are healthy: signed firmware, expected behavior, and normal traffic patterns. If a sensor starts chatting at odd hours, rate‑limit and flag it. Do you log anomalies today? Share your approach to ongoing verification below.
Passkeys based on FIDO2 remove guessable codes and shoulder‑surfable PINs. Your phone becomes the key, unlocking with a local biometric and cryptographic proof—no reusable secrets. If you’ve migrated from PINs to passkeys, what changed for your household guests and deliveries?

Private‑by‑Design Cameras and Doorbells
End‑to‑End Encryption Without Cloud Dependence
Footage can be encrypted from camera to viewer, with keys you control and optional local storage. Even if a server is breached, your videos remain unreadable. Which storage model—local NAS, encrypted hub, or hybrid—fits your comfort zone? Tell us your reasoning.
On‑Device AI That Forgets What It Sees
Person, package, or pet detection can run at the edge, storing only meaningful events and discarding raw frames. The model improves while personally identifiable data stays home. Have you noticed fewer false alerts with local AI? Share your before‑and‑after experience.
Neighborhood Sharing Without Oversharing
Redaction features blur faces and plates; access links can expire; consent prompts ensure transparency. Security thrives when communities collaborate thoughtfully. How do you balance being a good neighbor with respecting privacy? Comment with your favorite redaction or consent workflow.

Signed Updates You Can Trust
Look for devices that verify signatures, use secure boot, and prevent rollbacks to vulnerable versions. Scheduled maintenance windows reduce disruption and keep routines predictable. Do you prefer automatic updates or manual approval? Share your policy and why it works for your household.

Know What’s Inside with SBOMs
An SBOM lists software components, making vulnerabilities easier to track. When a library flaw hits the news, vendors with SBOMs respond faster. Would you consult an SBOM dashboard if your hub offered one? Tell us which risk signals you care about seeing first.

Resilience During Outages and Failures
When internet drops, critical controls should still function locally. Dual‑bank firmware and safe‑mode fallbacks reduce downtime. Have you tested your home’s offline plan? Walk through it this weekend and report what surprised you, so we can compile a community checklist.
Voice Assistants with Data Minimization
01
Tune sensitivity, require follow‑up confirmations for sensitive actions, and prefer on‑device wake processing when available. Fewer false activations mean less unintended recording. Have you customized wake settings for bedrooms versus kitchens? Share what cut accidental triggers without hurting responsiveness.
02
Standards like Matter enable lights, locks, and thermostats to respond locally, even if cloud services falter. Sensitive routines should not hinge on remote accounts. Which commands have you moved local, and what latency or reliability gains did you notice day‑to‑day?
03
Set short retention for voice clips, auto‑delete test recordings, and browse audit logs to confirm exactly what was captured. Transparency builds trust at home. If platforms offered monthly privacy reports, would you read them? Subscribe, and we’ll prototype a reader‑friendly template.